Methods to Secure Entry Shared Device Imperial Wins Casino Sign-In in New Zealand

When I think about using Imperial Wins Casino on a common gadget, security immediately crosses my mind. Using such a gadget presents major dangers, and I understand I need to be vigilant. It’s crucial to create a secure password and think about implementing 2FA, but that’s just the start. There are several methods to further safeguard my access. Let’s explore these crucial steps together.
Grasping the Threats of Shared Devices

While we frequently depend on shared devices for convenience, it’s crucial to comprehend the dangers involved. I know personally how easily our private data can become exposed when we use devices. Think about it: the login credentials and sensitive information you forget can be accessed by anyone who utilizes that gadget afterwards. That’s why I always remind myself to remain cautious. Unsecured Wi-Fi amplify this threat even more, subjecting us to possible hackers. Each time I access a shared gadget, I consider if I’m ready to risk my privacy. Taking control means understanding these dangers and remaining knowledgeable. We shouldn’t to neglect the potential outcomes of shared devices; it’s time to prioritize our security.
Establishing Strong and Distinct Access Codes
When it comes to developing strong and unique access codes, I want to highlight how important sophistication is. Using a passcode organizer has really transformed the process for me, facilitating to keep track of my passcodes. Moreover, I ensure to refresh them consistently, further enhancing my safety.
Significance of Complexity
Creating secure and individual passwords is essential for safeguarding our collective devices, especially since weak passwords can easily be compromised. I’ve learned the hard way that sophistication matters. Simple, foreseeable passwords are an easy target for hackers. By including a mix of letters, numbers, and special characters, I build obstacles that secure my accounts.
Using long passwords, ideally 12 digits or more, also increases security. I don’t depend on familiar phrases; instead, I construct random sequences that are harder to figure out. This unique approach not only safeguards my individual information but also gives me total control over who enters our shared devices. Remember, in an age of growing cyber threats, a intricate password isn’t just smart; it’s essential.
Utilizing Password Managers
A password manager can be a revolutionary tool for anyone seeking to create secure and distinctive passwords. I’ve found that it streamlines the intricate task of handling various passwords, making it simpler to stay safe. Instead of depending on memory or using a few alternatives, I let the manager generate random passwords that are hard to break. This way, I gain peace of mind knowing my accounts are secured.
What’s even more impressive is the simplicity it provides. With everything stored in one safe place, I don’t have to concern myself about forgetting passwords or reusing them across various sites. It empowers me to take control of my digital security, making sure that my private information stays private and protected.
Regular Password Updates
Even with a dependable password manager in place, routine password updates are crucial to maintaining security. I’ve found that altering my passwords every few months helps keep my accounts secure. I make sure my new passwords are robust, using a mix of letters, numbers, and symbols. Each one is distinct, so if one does get compromised, the others stay secure. It’s easy to fall into a pattern and use familiar passwords, but that’s a risk I’m not willing to take. I set notifications in my calendar to prompt changes, ensuring I stay prepared. Remember, it’s not just about making a strong password; it’s about keeping that strength fresh through frequent updates. Your security is worth the effort!
Enabling Two-Factor Authentication
Now that we’ve addressed developing resilient passwords, let’s talk about enabling two-factor authentication (2FA). I can’t highlight enough how advantageous 2FA is for boosting security on common devices. It adds an additional layer of protection that makes illicit access much challenging.
Benefits of Two-Factor Authentication
Why jeopardize your sensitive information when a simple step like two-factor authentication (2FA) can greatly improve your security? By adopting 2FA, you’re being proactive of your online safety. It adds an additional layer, ensuring that even if someone cracks your password, they can’t access your account without a additional verification step. This means you’re in command, making it much harder for possible intruders to compromise your data. Additionally, 2FA encourages peace of mind, knowing you’ve done everything possible to protect your information. With this additional protection, you can securely navigate common devices, lowering the risks linked to unapproved access. In a world where security is paramount, embracing 2FA is a prudent, simple move.
Steps to Enable 2FA
Having recognized the value of two-factor authentication (2FA) in securing your confidential information, it’s time to set it up on your accounts. First, log into your account settings where you’ll usually find a security section. Look for the option to enable 2FA; it might be called “Two-Step Verification” or something similar. Once you start the setup, you’ll likely choose between using an authenticator app or receiving SMS codes. If you opt for an app, download one like Google Authenticator or Authy and link it to your account by scanning the provided QR code. Complete the setup by inputting the code generated. Finally, be sure to save any backup codes in a secure location. You’re now more secure!
Clearing Browser History and Cache
When using a shared device, one often overlooks the necessity of clearing browser history and cache. I can’t stress enough how crucial this simple step is for maintaining your privacy. Every time I access my accounts or browse sensitive sites, I know traces are left behind. These remnants can expose my personal data to the next user. To clear browser history and cache, I navigate to the settings, often found under ‘Privacy’ or ‘History’. It’s as easy as clicking ‘Clear Data’, but the impact is significant. By doing this, I regain control over my information and ensure that no one can stumble upon my browsing habits. So, don’t skip this important step—protect your digital footprint effectively!
Using Private Browsing Mode
Private browsing mode can be a significant tool for anyone using a shared device. When I want to keep my online activities private, I activate this feature in my browser. It ensures that my browsing history, cookies, and cache aren’t stored once I close the session. This means no one else using the device later can easily access any of my information.
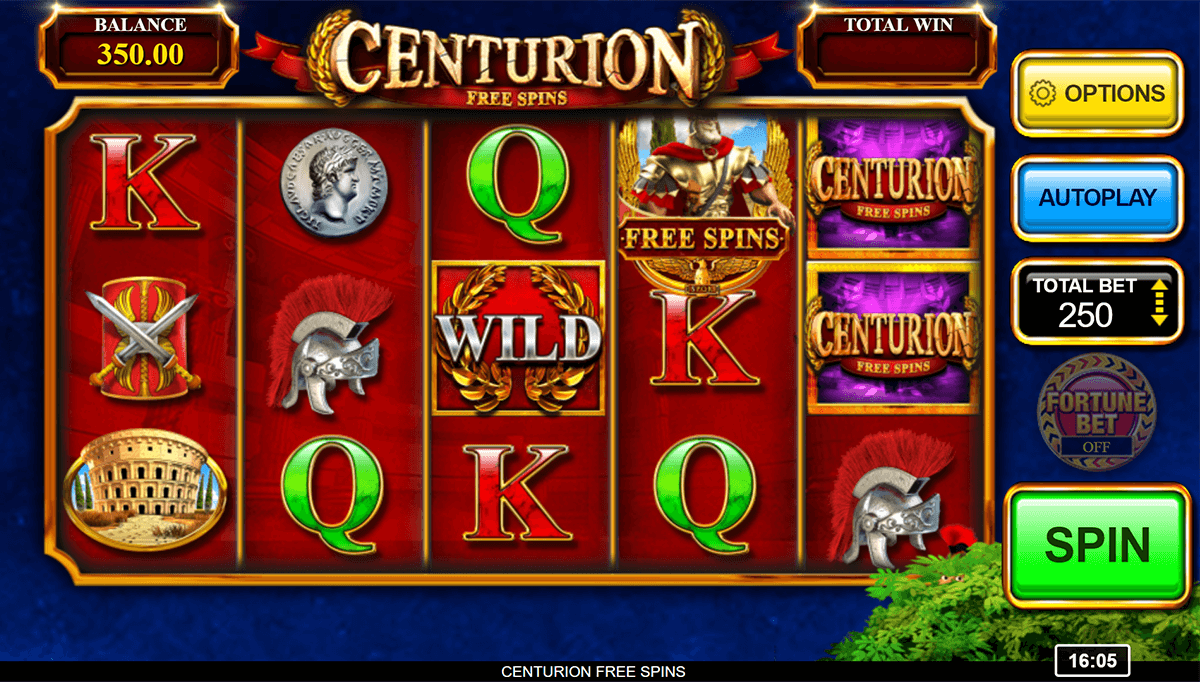
I consider it particularly beneficial when I’m accessing accounts, Imperial Wins Login Deposit Methods, especially sensitive ones like online casinos. With private browsing, I sense in control of my personal data, guaranteeing a more safe online experience. So, if you’re using a shared device and need to maintain your privacy, don’t skip this essential step—it can make a world of difference!
Logging Out After Each Session
Although it might seem like a hassle, logging out after each session is crucial when using a shared device. I can’t emphasize enough how important it is to take that extra moment to ensure your accounts remain secure. When I log out, I feel a sense of control over my information. It stops anyone from accessing my accounts, whether deliberate or accidental. Plus, it helps minimize the risk of someone changing my settings or making unauthorized transactions. If you consider it, logging out is a simple, effective step to safeguard your data. So, after I finish using the device, I always make it a point to sign out completely, confirming that my session is securely closed.
Keeping Your Software Updated
To keep your data secure, I always make a point to keep my software updated. I can’t emphasize enough how crucial it is to regularly check for updates on operating systems, applications, and security software. Developers constantly release patches that fix vulnerabilities, and ignoring these updates leaves your device exposed to potential threats.
I set reminders to run updates at least once a week. This proactive approach gives me peace of mind, knowing I’m in control of my security. Additionally, enabling automatic updates can save time and ensure my protection isn’t compromised. Remember, outdated software can be an open door for cybercriminals. Stay vigilant—keeping everything up to date is one of the simplest ways to protect your information!
Conclusion
In closing, securing entry to your Imperial Wins Casino profile on a shared computer is crucial to protect your information. By creating a strong password, activating two-factor authentication, and deleting your browser history, you can significantly lower your chance of unauthorized entry. Don’t forget to log out after each session and keep your software up-to-date. Following these easy steps, you’ll have a safer gaming experience while protecting your personal data. Remain vigilant and play responsibly!